By early next fall our district will begin to require staff users to use 2-Step verification in order to access their district Google accounts. A bit of background on what that is and an invitation to enable it prior to enforcement is the gist of this blog post.
[Note, the “2-Step verification” process may be known by other names like, “two-factor authentication” (2FA), or “multi-factor authentication (MFA)”.]
What is 2-Step verification?
2-Step verification adds a second layer of protection during the login process. Currently, your Google login is tied to “something you know” (your password). 2-Step verification adds a second layer of “something you have”, i.e., a mobile device, a phone number where you can be reached, a physical security key.
Why will we be implementing 2-Step verification?
Times are changing and hackers are finding new and creative ways to acquire user passwords: cyber hackers are buying lists of usernames and passwords on the dark web, they are using social engineering and email phishing tactics to steal passwords, they are also using something called “dictionary attacks” as a brute force method to guess weak passwords. Adding a second form of verification dramatically decreases the likelihood of your password, and consequently your account, being compromised. Additionally, school districts purchase cyber insurance which requires a regular review of security-related best practices/continuous improvement, and requiring an additional authentication method for account access is the next big push for districts to be compliant with cybersecurity risks/best practice.
How often will I need to use 2-Step verification?
Once you authenticate and complete the 2-step verification process and make sure to “remember this device” (their verbiage is Don’t ask again on this computer), Google will not require 2-step verification every time you log in. From that point on, Google will not prompt you to perform 2-Step verification on that device unless you clear your browser’s cache, change your password, it’s been around 30 days since your last verification and/or if Google suspects that your account has been breached.
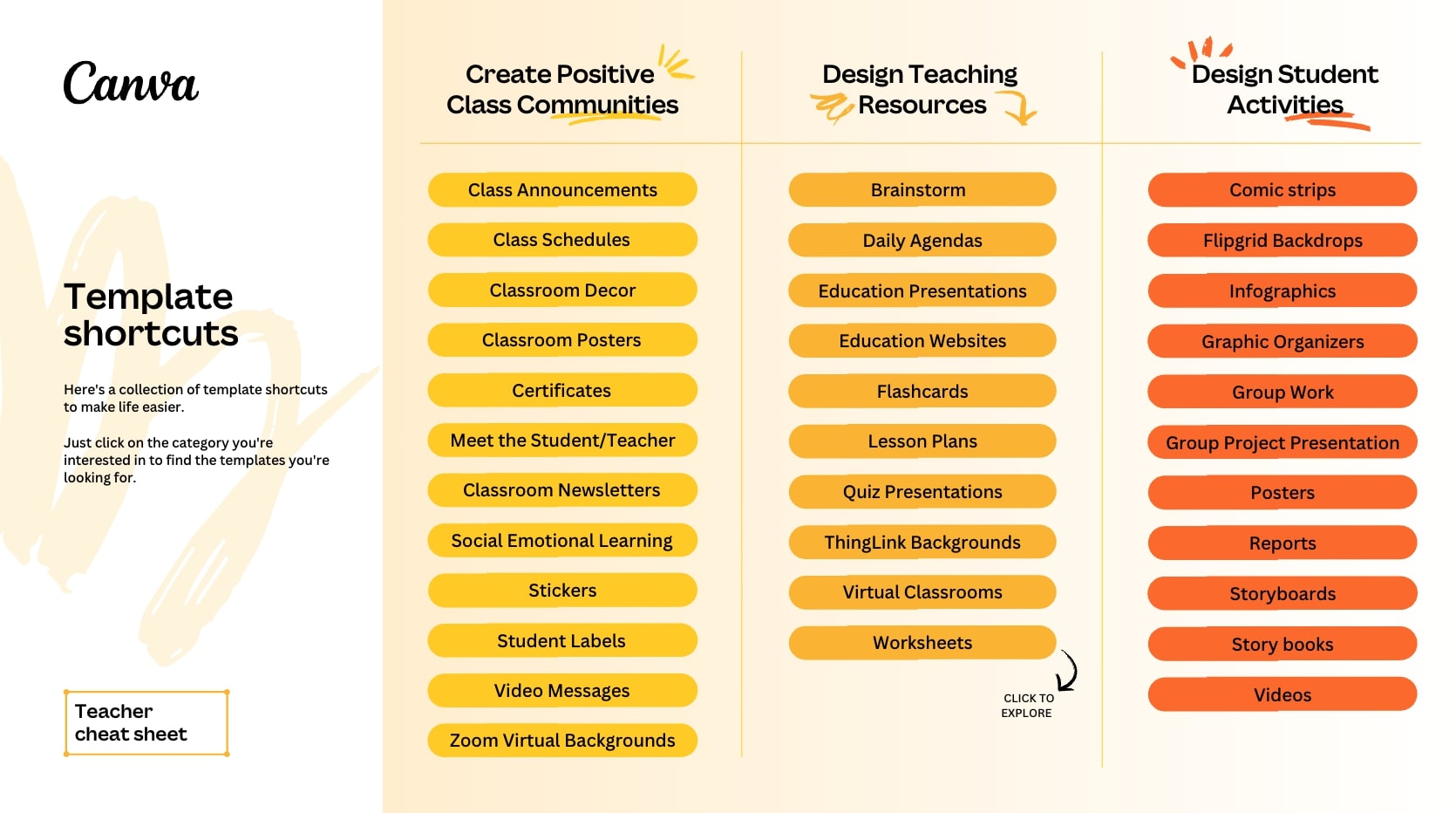
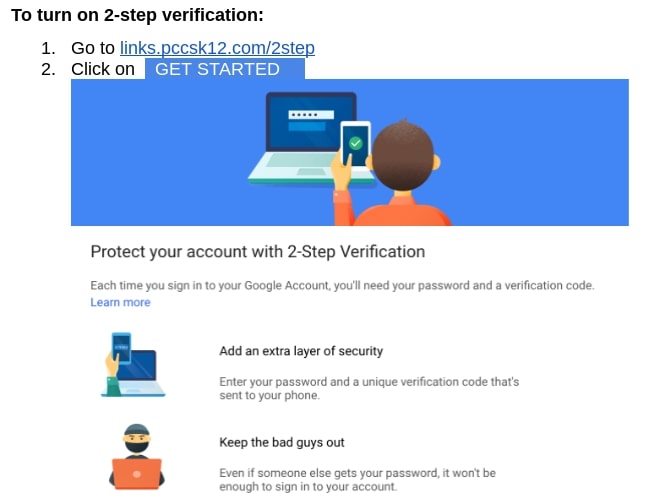
How do I enable 2-Step verification?
For guidance on how to enable 2-Step verification for your district account, visit http://links.pccsk12.com
See also https://support.google.com/accounts/answer/185839 AND https://safety.google/authentication/
————–
To make more secure other accounts you have (banking, Apple, Amazon, any other online retailers, especially ones with your credit card info, personal email, etc.), consider also enabling 2-Step verification if it isn’t already in place. Basically any account that would be a real bummer to have someone else you don’t sanction gain access to.
————–
Expect more details in future blog posts around this topic.





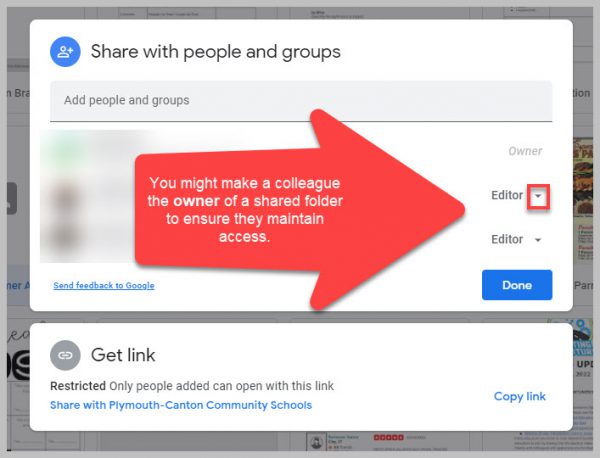
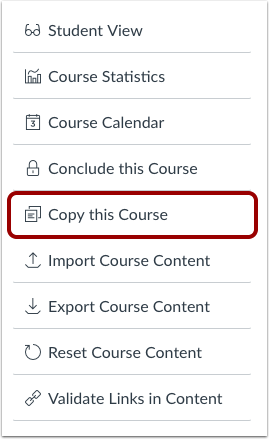 If you want to share your course with another teacher, you can
If you want to share your course with another teacher, you can