Our cell phones are threatened by bad actors more than many of us may realize. Below are the most common and critical mobile security threats and a short synapse of examples and ways to safeguard against attack..
4 Different Types of Mobile Security Threats
Mobile security threats are commonly thought of as a single, all-encompassing threat. But the truth is, there are four different types of mobile security threats that we need to take steps to protect ourselves from:
- Mobile Application Security Threats. Application-based threats happen when people download apps that look legitimate but actually skim data from their device. Examples are spyware and malware that steal personal and business information without people realizing it’s happening.
- Web-Based Mobile Security Threats. Web-based threats are subtle and tend to go unnoticed. They happen when people visit affected sites that seem fine on the front-end but, in reality, automatically download malicious content onto devices.
- Mobile Network Security Threats. Network-based threats are especially common and risky because cybercriminals can steal unencrypted data while people use public WiFi networks.
- Mobile Device Security Threats. Physical threats to mobile devices most commonly refer to the loss or theft of a device. Because hackers have direct access to the hardware where private data is stored, this threat is especially dangerous.
Below are the most common examples of these threats, as well as steps to can take to protect ourselves from them.
1. Social Engineering
Social engineering attacks are when bad actors send fake emails (phishing attacks) or text messages (smishing attacks) in an effort to trick someone into handing over private information like their passwords or downloading malware onto their devices.
Reports by cybersecurity firm Lookout and Verizon show a 37% increase in enterprise mobile phishing attacks and that phishing attacks were the top cause of data breaches globally in 2020.
Phishing Attack Countermeasures
The best defense for phishing and other social engineering attacks is to teach youself how to spot phishing emails and SMS messages that look suspicious and avoid falling prey to them altogether.
2. Data Leakage via Malicious Apps
85% of mobile apps today are largely unsecured. Tom Tovar, CEO of Appdome, says, “Today, hackers can easily find an unprotected mobile app and use that unprotected app to design larger attacks or steal data, digital wallets, backend details, and other juicy bits directly from the app.”
For example, when someone visits Google Play or the App Store to download apps that look innocent enough, the apps ask for a list of permissions before people are allowed to download them. These permissions generally require some kind of access to files or folders on the mobile device, and most people just glance at the list of permissions and agree without reviewing them in great detail.
However, this lack of scrutiny can leave devices vulnerable. Even if the app works the way it’s supposed to, it still has the potential to mine corporate data and send it to a third party.
How to Protect Against Data Leakage
Review permissions carefully and typically avoid third-party apps.
3. Unsecured Public WiFi
Public WiFi networks are generally less secure than private networks because there’s no way to know who set the network up, how (or if) it’s secured with encryption, or who is currently accessing it or monitoring it.
For example, cybercriminals often set up WiFi networks that look authentic but are actually a front to capture data that passes through their system (a “man in the middle” attack).
If this seems far-fetched, it isn’t. Creating fake WiFi hotspots in public spaces with network names that look completely legit is incredibly simple, and people are very willing to connect, as shown by experiments run at the Democratic and Republican conventions in 2016 and by an experiment run by a researcher in 2019 from Magic.
How to Reduce Risks Posed By Unsecured Public WiFi
Avoid connecting to public networks as much as possible, confirm they are legit, and do not conduct any sensitive activity while on them.
4. Spyware
Spyware is used to survey or collect data and is most commonly installed on a mobile device when users click on a malicious advertisement (“malvertisement”) or through scams that trick users into downloading it unintentionally.
Whether you have an iOS or Android device, these devices are targets ripe for data mining with spyware—which could include your personal as well as our district data if that device is connected to our network.
How to Protect Against Spyware
Dedicated mobile security apps (like Google’s Play Protect) can help you detect and eliminate spyware that might be installed on your devices. Ensuring you keep your device operating systems (and applications) up to date also helps ensure that your devices and your data are protected against the latest spyware threats.
5. Poor Password Habits
A 2020 study by Balbix found that 99% of the people surveyed reused their passwords between work accounts or between work and personal accounts. Unfortunately, the passwords that employees are reusing are often weak as well.
How to Reduce or Eliminate Mobile Password Threats
The NIST Password Guidelines are widely regarded as the international standard for password best practices. Following these guidelines will help protect you against threats from weak or stolen passwords. Password managers can simplify the work required to follow these guidelines.
Using more than one authentication factor (multi-factor authentication or MFA) to access mobile applications will also help reduce the risk that a bad actor could gain access to your systems since they’d need to verify their identity with additional authentication factors in order to log in.
Finally, implementing passwordless authentication will help you eliminate password risks altogether. For example, in the event that a mobile device is stolen or accessed illegally, requiring a facial scan as a primary (or secondary) authentication factor could still prevent unauthorized access.
6. Lost or Stolen Mobile Devices
Lost and stolen devices remain a threat.
How to Protect Against Lost or Stolen Device Threats
First and foremost, you’ll want to know what steps to take if you lose your device. Since most devices come with remote access to delete or transfer information, that should include asking you to make sure those services are activated.
7. Out of Date Operating Systems
Like other data security initiatives, mobile security requires continuous work to find and patch vulnerabilities that bad actors use to gain unauthorized access to your systems and data.
However, these patches only protect if you keep your devices up to date at all times.
 ——–
——–
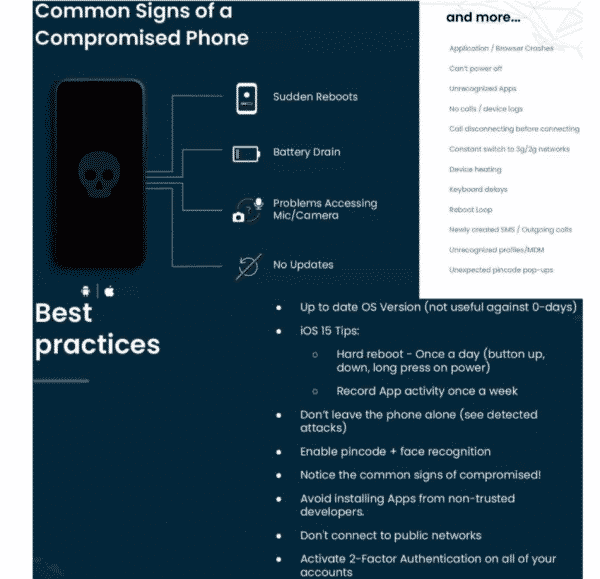
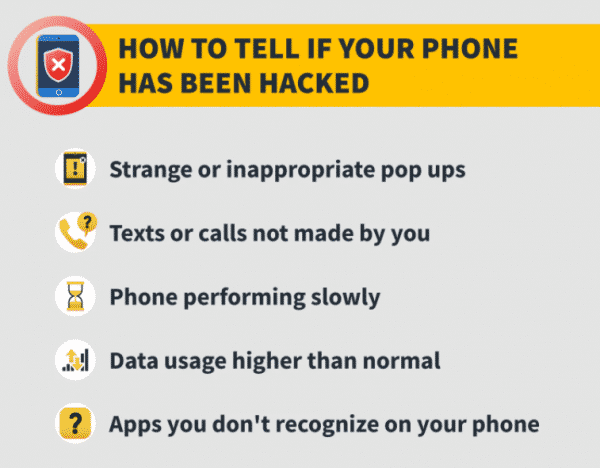
See the pic below for common signs of a compromised phone and a recap of best practices to avoid falling prey.